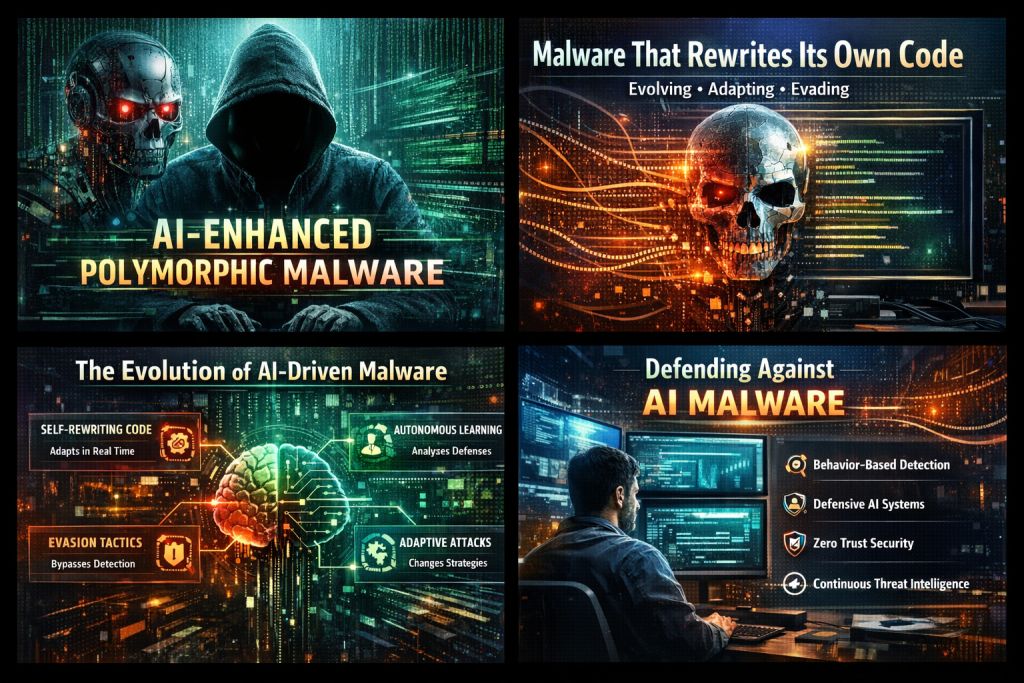
When Malware Starts Thinking: The Rise of AI-Driven Polymorphic Attacks
For a long time, cybersecurity worked in a predictable way. Hackers created malware, security teams found it, patches were released, and then everyone prepared for the next threat.
That cycle is now being disrupted.
Now, a new type of malware is appearing. This software doesn’t just follow instructions—it adapts as it runs. With artificial intelligence, these threats change themselves in real time, learning which tactics succeed and which fail.
This is known as AI-enhanced polymorphic malware, and it could be one of the biggest changes in cybercrime in decades.
Malware That Refuses to Stay the Same
Traditional polymorphic malware could already change its appearance. Each copy appeared different, which made it harder for antivirus tools to detect.
The key difference lies in how these changes occur.
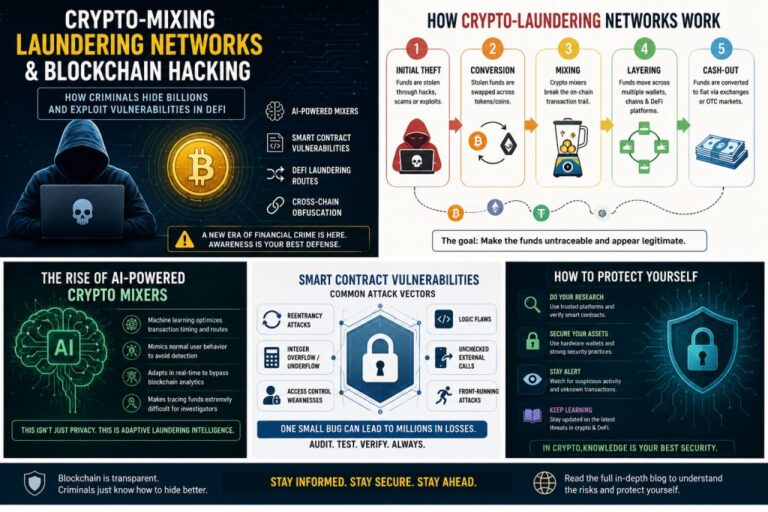
Instead of just following preset rules, newer versions use machine learning to decide what to change. Some try out different behaviours. Others rewrite parts of their own code as they run. Some even use cloud-based AI to create new payloads whenever needed.
Put simply, the malware is testing its environment.
If something triggers an alert, the malware tries another method. If one route doesn’t work, it looks for other options. Over time, it develops its own way to survive.
This is a big step forward compared to older, unchanging threats.
A Moment That Made Me Pay Attention
Not long ago, I helped investigate a case where the same network kept getting infected. Each alert seemed unrelated, with different file hashes, different ways of running, and different traces left behind.
It first appeared that multiple attackers were involved.
But after looking more closely, we found it was just one malware family that kept changing itself after every cleanup. The antivirus system kept seeing each version as a new threat.
That case stuck with me—and it happened before AI was involved.
If regular polymorphic malware could already confuse defences so much, just think what will happen when malware starts to learn.
How AI Changes the Game
AI-driven malware doesn’t just hide itself. It also studies how systems respond.
Some experimental threats have shown the ability to:
- Delay activity when they sense virtual machines
- Modify system calls to avoid behaviour monitors
- Change network patterns to blend in
- Generate new components when old ones are blocked
Researchers have even shown malware that can rewrite its own source code using large language models.
Instead of coming in fully formed, these threats change and adapt inside the systems they infect.
That’s what makes them so dangerous.
Why This Matters More Than You Think
Signature Detection Is Losing Ground
Most security tools rely on known patterns, but adaptive malware lacks fixed signatures, making each version appear different.
Security can’t just look for fingerprints now. It needs to understand what the malware is trying to do.
Attackers Don’t Need Advanced Skills
AI tools make things easier for attackers. Now, even people with little experience can create phishing emails, modify malware, or automate attacks.
This leads to more threats, coming faster and from more sources.
Persistence Becomes Smarter
Some malware now tests defences like a chess player, adapting its approach when moves fail, or it detects observation.
Sheer brute force is no longer the main tactic.
Now, it’s about strategy.
The Rise of Autonomous Threats
Many experts are worried not just about malware hiding itself, but about it acting on its own.
We’re approaching malware that can:
- Select targets on its own
- Decide when to activate
- Spread selectively
- Remain dormant until conditions improve
Once these threats are released, they may not need much help from people.
This demands a fundamental shift in incident response.
Fighting Back: What Actually Works
Even with all the news, defenders still have options.
Here’s where modern security is heading.
Behaviour Over Appearance
Instead of just scanning files, advanced systems now watch what programs do:
- Unexpected privilege changes. Memory abuse. Strange process chains. Odd network behaviour.
- Code can keep changing, but behaviour stays the same.
Defensive AI
Security platforms now use machine learning to analyse large volumes of data from devices and networks.
They look for patterns that people might miss, such as small timing changes, unusual ways of accessing files, or rare combinations of system calls.
It’s AI vs. AI.
Zero Trust Architecture
No device is trusted by default. Every request has to be checked.
This limits how far attackers can move and helps contain damage in the event of a breach.
Adaptive malware has a harder time in tightly separated networks.
Continuous Intelligence
Defences that never change don’t work well against attackers who keep evolving.
Today’s security teams depend on regular threat updates, behaviour clues, and shared research.
Security isn’t just a product anymore. It’s an ongoing process.
Least Privilege
Most attacks succeed because systems grant too much access.
By reducing permissions, you limit what malware can do, even if it gets in.
Practical Advice for Organisations
If you’re planning a security strategy today:
- Focus on behavioural detection
- Monitor internal traffic, not just external
- Train employees on modern phishing
- Segment critical assets
- Test response plans regularly
- Design systems assuming compromise will happen
Prevention is important, but containing threats is even more critical.
Final Thoughts: A Quiet Arms Race
AI-powered polymorphic malware marks a major turning point.
We’re facing attackers who can quickly adapt and evade defences.
Attackers are trying new things, researchers are working to keep up, and defenders are rethinking their whole approach.
This extends beyond traditional cybersecurity concerns.
It’s a contest of intelligence. The organisations that succeed won’t be the ones with the flashiest tools.
Key takeaway: The real advantage will belong to the organisations that adapt and learn faster than attackers.
One Last Takeaway
Malware can now act on its own, stick around, and change itself. Our response needs to be just as flexible.
Cybersecurity is no longer static.
Neither are the threats.