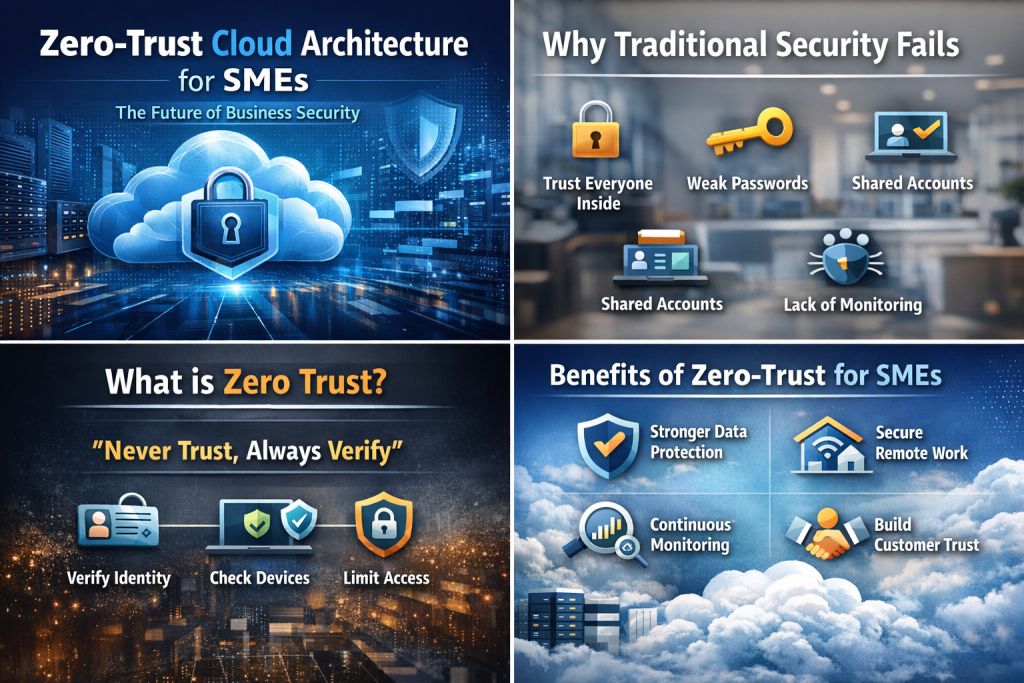
Zero-Trust Cloud Architecture for SMEs: Why This Security Model Is Now Essential
Business security used to be simple. You locked the office, installed antivirus software, and trusted everyone on your network. This approach worked until companies moved to the cloud and employees started working from different locations.
Now, most small and medium businesses (SMEs) use cloud tools for email, payments, customer data, and daily work. Still, many rely on old security habits that trust users as soon as they log in.
This mindset is now one of the biggest risks for SMEs.
That’s why Zero-Trust Cloud Architecture is important. It’s more than a buzzword—it’s a practical way to protect businesses today.
The Old Security Model Is Breaking
I’ve spoken to many small business owners who say something like:
“We’re not big enough for hackers to care about us.”
Thinking this way can be more dangerous than any computer virus.
Hackers don’t just target big companies anymore. They look for easy targets. Small businesses often have weaker security, fewer checks, and less monitoring.
In the old model:
- Once you log in, you are trusted
- Internal users get broad access
- Devices are rarely checked
- Suspicious activity often goes unnoticed
This old way doesn’t work in cloud environments now.
What Zero Trust Really Means (In Simple Words)
Zero trust is based on one idea:
- No one is trusted automatically. Not at any time.
It doesn’t matter if:
- The user is an employee
- The device is inside the office
- The request comes from a known location
Every time someone tries to access something, the system checks them each time.
In a cloud setup, this means:
- Identity is checked every time
- Devices must meet security rules
- Access is limited to only what’s needed
- Activity is constantly watched
Global security groups like NIST recommend this approach, and many cloud-based companies already use it.
Why SMEs Are Being Targeted More Than Ever
I’ve seen this happen many times.
Picture a small company using cloud email and storage. An employee clicks a fake email link, and their login details get stolen. The attacker logs in, and because the system trusts internal users, they can access shared files, customer data, and financial documents.
No alarms. No warnings.
The company only realizes there’s a problem when customers complain or money goes missing.
This isn’t unusual. It happens every day.
Real Experience: A Lesson That Changed My View on Security
I once worked with a small service company of fewer than 25 employees. They did everything in the cloud—email, documents, accounting, and CRM. They thought the cloud provider handled all their security.
One employee left, but their access wasn’t fully removed. Months later, someone used that unused account. No special hacking skills were needed, just access that should have been removed.
The damage wasn’t large, but the stress was. The founder told me:
- “I thought security was something we’d deal with later.”
That moment stayed with me. Security isn’t something you can delay anymore.
How Zero-Trust Cloud Architecture Fixes These Issues
1. Identity Comes First
Zero trust begins with identity.
Instead of relying only on passwords, it uses:
- Multi-factor authentication
- Identity verification services
- Central access control
Even if someone gets a password, they still need extra proof to get in.
This single change prevents many attacks.
2. Access Is Limited on Purpose
In many SMEs, people can access things they don’t need, often just for convenience.
Zero trust stops that habit.
Employees only get access to what they need for their job, nothing more.
If one account is compromised, the damage stays limited.
3. Devices Must Prove They’re Safe
Zero trust checks both people and devices.
Before access is allowed, the system looks at:
- Software updates
- Security settings
- Basic protection tools
If a laptop isn’t safe, it doesn’t get access. It’s simple.
This stops many ransomware attacks before they start.
4. Remote Work Becomes Safer
Remote work is helpful, but it can create security gaps if not managed well.
Traditional VPNs trust users once they connect. Zero trust does not.
Instead:
- Each app is protected separately
- Every session is verified
- Unusual behavior triggers alerts
This approach makes remote access safer and easier.
5. Constant Monitoring, Not Blind Trust
Zero trust systems monitor activity all the time.
If someone logs in at unusual times, downloads large files suddenly, or accesses data they never used before, the system notices.
This approach follows global security guidelines, such as the NIST Zero Trust Architecture, which emphasizes continuous verification.
Why Cloud Platforms Support Zero Trust So Well
Cloud systems are built for flexibility, making them a good fit for zero trust.
They already offer:
- Identity-based access
- Detailed activity logs
- Automation tools
- Scalable security controls
For SMEs, this means strong security without large upfront costs.
You don’t need a large IT team. You just need smart controls.
A Situation That Truly Changed My Perspective
A small healthcare startup once told me how stressed they felt after a data incident. It wasn’t caused by malware or hacking tools; it was just poor access control.
After switching to a zero-trust setup:
- Access was tied to identity
- Ex-employees lost access instantly
- Every action was recorded
Months later, the founder said something simple but powerful:
- “We finally feel in control.”
That simple statement highlights the real value of zero trust.
Is Zero Trust Too Complicated for Small Businesses?
People often ask this question, and the honest answer is no.
Modern zero-trust tools are:
- Cloud-based
- Subscription-friendly
- Easier to use than older systems
SMEs can begin with small steps:
- Enable multi-factor authentication
- Protect important cloud apps
- Review access regularly
- Monitor basic activity logs
Zero trust isn’t about being perfect. It’s about making steady progress.
Trusted Experts Agree on This Direction
Zero trust is supported by:
- National cybersecurity standards
- Cloud security leaders
- Enterprise and SME-focused frameworks
It’s not just a passing trend. This is the direction security is moving.
Why Zero Trust Is the Future of SME Security
Cyber threats will keep changing. Trust-based systems won’t last much longer.
For SMEs, zero trust means:
- Fewer surprises
- Better control
- Safer remote work
- Stronger customer confidence
The future of business security isn’t about locking everything down.
It’s about smart verification, limiting access, and staying alert.
For small businesses using the cloud, zero trust isn’t just the future. It’s the safest path forward.