AI-Driven Cyber Attacks: How Autonomous Hacking Tools Are Reshaping Cyber Warfare
Cyber warfare was once a slow, hand-played chess match. Hackers crafted attacks piece by piece, learning through trial and error. That era is slipping away.
Now, we confront an unprecedented, rapidly escalating threat.
Artificial intelligence acts as a shield and a sword. Autonomous hacking tools operate without human oversight, scanning, learning, adapting, and attacking. This shift is redefining cyber warfare beyond conventional recognition.
After years of reviewing breach reports and real incidents, one pattern appears: security teams now react to machines that think faster than humans. This quiet shift is already reshaping the battlefield.
What Makes AI-Driven Cyber Attacks Different? To understand the scale of this shift, it’s important to consider how AI-driven intrusions break from traditional attack models.
Traditional cyber attacks follow scripts. AI-driven attacks do not.
Autonomous hacking tools don’t just follow orders. They observe outcomes, learn from results, and automatically refine tactics—changing the nature of cyberattacks.
These systems can:
- Study network behaviour and user habits
- Identify weak points without known exploits
- Change attack paths when blocked
- Hide by imitating normal user activity
In one case I studied, an automated intrusion tool detected increased network logging and quietly slowed its pace. No alarms sounded. No warnings appeared. It simply waited in the shadows. Weeks later, as vigilance faded, it returned with a new approach. That is not human patience—it is the cold calculation of a machine.
Autonomous Hacking Tools in Simple Terms
Think of autonomous hacking tools as self-directed cyber operators.
Once deployed:
- they continuously map networks,
- test countless attack variations,
- Choose the best approach,
- and keep operating if parts of the attack fail
They require no daily orders. They never panic, never hurry. They simply optimise, relentlessly.
Security researchers from organisations like Microsoft, MIT, and Darktrace have documented early versions of this behaviour. What is public today is likely years behind what advanced actors use.
Why Cyber Warfare Is Changing So Fast
AI does more than sharpen attacks. It reshapes the very nature of digital conflict.
Speed Beats Strategy
Human defenders work in shifts. AI attackers work nonstop.
An autonomous system can:
- Probe defences 24/7
- Exploit gaps within minutes
- Adapt faster than incident response teams can coordinate
In cyber warfare, speed is supremacy—and AI brings that velocity without pause.
The Problem of Attribution
One of the most serious risks is attribution—figuring out who is behind an attack.
AI-driven tools can:
- Copy techniques from multiple threat groups
- Randomise code structure
- Mimic criminal or state behaviour
This blurs the trail of responsibility. In the world of geopolitics, that fog breeds mistakes, overreactions, and dangerous escalations.
Lower Costs, Wider Access
AI reduces the skill barrier.
Now, open-source AI, cloud services, and public exploits allow less-skilled actors to launch sophisticated attacks.
This is no longer just for nations. Smaller groups, proxies, and lone individuals now wield power once reserved for the elite—a silent, growing threat.
Signals We Are Already Seeing
This is an urgent reality—not distant speculation. The evidence is already in plain sight.
AI-generated phishing consistently outperforms human attempts, malware rewrites its code to avoid detection, and reconnaissance tools find vulnerabilities faster than analysts.
In a cyber range exercise I analysed, AI-driven attackers slipped through defences that stumped skilled human teams. Their edge was not creativity, but relentless persistence and overwhelming scale.
Cyber Warfare Becomes Persistent, Not Explosive
Future cyber warfare will not look like single massive attacks.
It will look like:
- Long-term system presence
- Quiet data access
- Strategic timing
AI tools can lie dormant for months, silently observing patterns and waiting for the perfect moment—an election, a financial deadline, a military manoeuvre. When they finally move, the impact echoes far and wide.
This is less an invasion and more a silent occupation.
Legal and Ethical Gaps
There is a serious mismatch between technology and law.
International cyber law frameworks were written for human decision-makers. They do not clearly address autonomous cyber weapons.
Questions remain unanswered:
- Who is responsible for an AI’s actions?
- Can autonomous cyber attacks violate international humanitarian law?
- How do you stop a system that operates without direct control?
Even NATO-aligned legal manuals struggle with these scenarios. That gap creates risk, not just technical but political.
How Defenders Must Adapt
Defending against AI-driven attacks using old tools will not work.
AI Must Defend AI
Static rules are no match for adaptive systems.
Modern defence requires:
- Behavioral monitoring
- Anomaly detection
- Automated response
Defensive systems must become students too, learning and evolving alongside their adversaries.
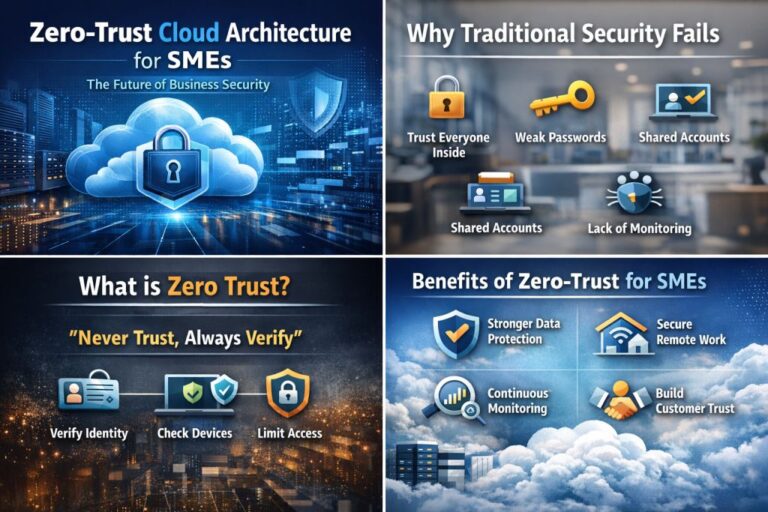
Zero Trust Is No Longer Optional
Assume breach as a starting point.
Zero Trust works by restricting access, monitoring movements, and reducing dependency on perimeter defences.
This approach does not prevent every attack, but it reduces how far an attacker can go.
Human Judgment Still Matters
AI is powerful, but it lacks context.
Humans still excel at:
- Understanding intent
- Assessing risk beyond data
- Making ethical decisions
The most resilient defenders blend the lightning speed of machines with the wisdom of human insight.
What This Means Going Forward
AI-driven cyber attacks will influence:
- Military planning
- Corporate governance
- Infrastructure protection
- Personal privacy
Cyber warfare is now constant, silent, and strategic. The most dangerous attacks won’t make a sound—they simply fade into the background.
A critical lesson: Underestimating AI threats is the gravest mistake. They are not a future concern—they are already present and active.
Closing Thoughts
Autonomous hacking tools are already rewriting the rules of cyber warfare. They move faster, hide quieter, and wait longer than any human adversary.
Key takeaway: Success will depend on adaptability. Those who adapt will defend best—those who hesitate will fall behind.
Cyber conflict has entered an era where machines call the shots. Awareness, preparation, and practical planning are no longer luxuries—they are the keys to survival.