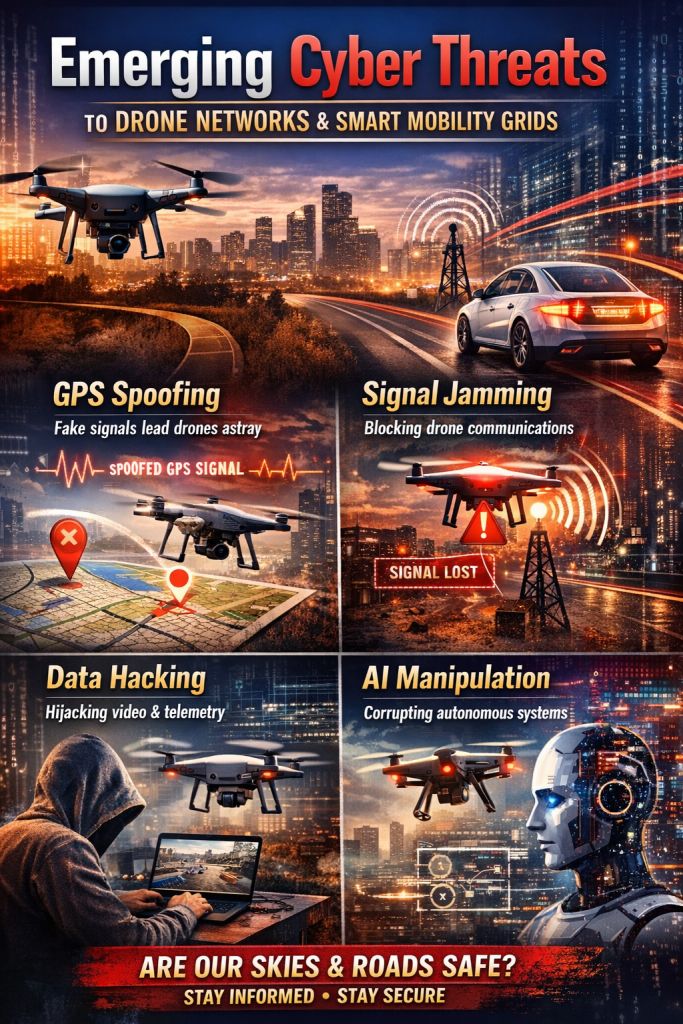
New Cyber Threats Facing Drone Networks and Smart Mobility Grids
Looking Closer at the Risks We Often Overlook
Just a few years ago, drones and smart mobility systems felt like science fiction. Today, they’re part of everyday life—delivering medicine, managing traffic, scanning farms, surveying construction, and helping rescue teams. This shift happened so quickly that most people never paused to ask a key question: What if these networks are attacked?
I hadn’t thought much about this myself until an incident a few years ago changed my perspective. During a drone test, one unit suddenly drifted to the side, as if it had been pushed. The pilot insisted they hadn’t touched the controls. We later discovered the drone had picked up confusing GPS signals from outside. It wasn’t an attack; it was just interference, but it still made the drone behave unpredictably. That experience made me realize how fragile these systems can be.
Most people never hear stories like this.
As drones and mobility networks spread, their weaknesses grow too. Cyberattacks on these systems aren’t just a future concern; they’re already happening and getting more advanced each year.
Why These Systems Have Become Such Easy Targets
Drones and smart mobility grids depend almost entirely on connected systems. In these cases, the digital and physical worlds blend together. Even a small digital breach can cause real problems, like drones going off course, self-driving cars stalling, traffic jams, or emergency services being disrupted.
Hackers are drawn to these systems for several reasons:
- Their communication is mostly wireless
- Many use outdated or unencrypted data links
- They depend heavily on cloud services
- APIs and third-party integrations often create blind spots
- Automated systems react instantly, even to bad data
With rapid global adoption, it’s easy to see why attackers view this as a growing opportunity.
1. GPS Spoofing: Quiet, Subtle, and Surprisingly Effective
This is one of the easiest attacks to pull off, but also one of the hardest to notice right away. Instead of hacking the drone directly, attackers fool its navigation by sending fake coordinates.
When a drone receives false GPS data, it might:
- Wander into restricted airspace
- Land somewhere, it shouldn’t
- Fly miles off course
- Behave as if it’s “drunk in the sky.”
The incident I witnessed was minor compared to what’s possible. Some researchers have shown that equipment costing just a few hundred dollars can fool entire groups of drones. The risk isn’t just about lost deliveries—it’s also about what could happen if emergency drones, surveillance units, or industrial fleets are taken over during their missions.
2. Signal Jamming: Cutting Communication at Its Core
While spoofing changes signals, jamming simply blocks them. It’s like shouting so loudly that no one else in the room can hear.
When communication links collapse, drones may:
- Trigger emergency landings
- Lose video feed
- Stop responding to commands
- Drift without guidance
- Drop offline entirely
At a smart mobility demonstration I attended, a nearby transmitter disrupted half the fleet, making them freeze in mid-air. No one expected that simple radio interference could cause so much trouble.
3. Hijacking Video Streams and Data Feeds
Many drones, especially older or less expensive ones, still send video without proper encryption. This means anyone nearby with the right tools can quietly watch:
- Live surveillance footage
- Mapping images
- Delivery routes
- Infrastructure scans
I’ve watched security researchers do this with surprising ease. They tuned into an unprotected drone feed as easily as flipping through TV channels. It’s unsettling, especially considering how many drones handle sensitive tasks.
4. Malware Tailored for Smart Mobility Systems
Most people think malware only affects phones or laptops. But the threat has changed. Now, harmful code is designed specifically for:
- Drone control apps
- Smart traffic systems
- Cloud mobility platforms
- Navigation units in autonomous vehicles
- Charging networks
A well-known experiment called “SkyJack” used a drone to take over other drones in flight by exploiting weaknesses in Wi-Fi. The research wasn’t meant to cause harm, but it proved that airborne malware is now a real possibility.
5. Weak or Exposed APIs
Smart mobility systems rely heavily on APIs. These connect everything— from traffic lights and charging stations to fleet dashboards and delivery drones.
But poorly secured APIs can allow attackers to:
- Extract real-time location data
- Override vehicle routes
- Access user details
- Disable critical sensors
- Push false commands into the system
Researchers found weaknesses in an international EV charging network that allowed attackers to track vehicles, view sessions, and remotely shut down chargers. If this happens with drones or self-driving vehicles, the risks could grow fast.
6. Cloud System Breaches
Many people don’t realize that drone fleets and mobility grids rely on cloud systems for almost everything—mapping, commands, routes, data logs, and firmware updates.
If someone breaches the cloud dashboard, they can:
- Monitor entire fleets
- Interrupt ongoing missions
- Alter navigation instructions
- Extract sensitive footage
- Inject malicious updates
I once spoke with a mobility analytics team that noticed strange login attempts in their cloud account. It turned out to be an internal audit, but the experience showed how quietly these breaches can happen.
7. Manipulating the AI That Powers Automated Systems
The most unsettling threat is that you don’t have to hack the drone or vehicle itself. You just need to manipulate the AI that controls it.
Attackers can confuse AI by:
- Feeding it corrupted training data
- Using adversarial images
- Faking sensor input
- Creating patterns, the system misreads
One study found that affixing a small sticker to a stop sign caused an AI-powered car to completely ignore it. Drones, which rely even more on computer vision, have the same weaknesses.
8. Supply Chain Attacks: The Hidden Backdoor
Modern drone and mobility systems aren’t made by just one company. They’re built by dozens or even hundreds of suppliers working together.
This means vulnerabilities can hide in:
- Firmware updates
- Sensor modules
- Third-party libraries
- IoT components
- Vendor dashboards
A small security flaw hidden in a component’s code can become a major breach when it’s used in thousands of devices.
What We Can Do to Protect These Systems
The good news is that while these threats are serious, solutions are improving quickly. Some of the most effective steps are:
1. Encrypting communication channels
It’s a basic requirement, but many systems still skip it.
2. Using multi-signal navigation
Using GPS along with visual, inertial, and satellite alternatives helps reduce spoofing risks.
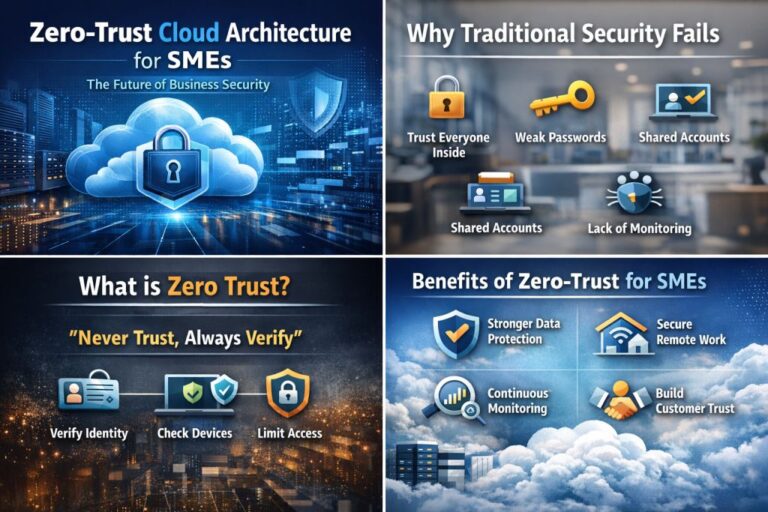
3. Adopting zero-trust security frameworks
Every device, user, and signal should verify itself at every step.
4. Deploying AI-based anomaly detection
These tools can spot unusual behavior long before a human operator would notice.
5. Conducting regular penetration testing
Ethical hackers can help find vulnerabilities that others might miss.
6. Hardening cloud infrastructure
This is important because a cloud breach can take down everything at once.
Final Thoughts
Drones and smart mobility grids aren’t just futuristic gadgets anymore. They’re becoming the backbone of logistics, security, transportation, and emergency services. But as we rely on them more, the risks grow too. Cyberattacks on these systems don’t just disrupt data—they can disrupt entire cities.
The technology itself isn’t the problem. The real issue is a lack of awareness.
We’re entering a time when cybersecurity will determine how safe our movement is, both on the ground and in the air. The sooner we take these threats seriously, the better prepared we’ll be as mobility becomes fully automated.