Data Privacy, Tech Law & Digital Policy: Navigating the New Rules of the Digital Age
Technology rapidly evolves as laws strive to keep up. Governments, businesses, and citizens face challenges: protecting rights, enabling innovation, and managing geopolitical risk. This blog highlights developments and offers practical steps you can take—today—to help your organization or yourself stay compliant, secure, and ready for the future.
1. The global AI regulation race: why it matters now
Regulation is now a global race. The EU’s AI Act sets comprehensive, strict rules for high-risk AI, impacting global standards for transparency, governance, and penalties.
The U.S. pursues a mixed strategy: executive orders, agency guidance, and voluntary standards like NIST’s AI RMF, focusing on innovation and risk management.
Why this matters for businesses: If you operate globally, design AI compliance as an international program. Classify risk, document datasets and decisions, conduct model audits, and map regulatory requirements for each market.
2. India’s DPDP Act vs. U.S. approaches — different paths, shared problems
India’s DPDP Act (2023) sets a digital data framework, covering fiduciary duties and cross-border matters. It supports India’s growing digital policies on data localization and platform accountability.
The U.S. mixes federal and state rules. Without a unified law, agencies and White House set standards. Businesses must navigate diverse global rules.
Recommended actions: Maintain a single source of truth, such as a comprehensive data inventory and a transfer matrix (a tool that tracks how data moves and where it is stored). Implement Data Protection Impact Assessments (DPIAs) to assess data risks for higher-risk processing, and integrate privacy-by-design (building privacy protections into products from the start) into product development roadmaps.
3. Digital sovereignty: countries building their own internet ecosystems
Digital sovereignty means countries control data, platforms, and tech stacks. China, the EU, and India drive local governance and data localization as part of national security and economic plans, shaping technical standards and infrastructure.
For companies: Plan for multicloud and multi-region deployments, modularize services to comply with local data residency requirements, and separate personal data storage to reduce cross-border exposure.
4. Surveillance tech vs civil liberties: where do we draw the line?
Biometrics and predictive policing aid safety but can also raise concerns about discrimination and free speech. Civil groups push for limits on biometric surveillance and greater transparency in contracts.
Balance checklist for policymakers:
- Require independent impact assessments and judicial oversight for surveillance deployments.
- Publish vendor contracts and technical specs where possible.
- Limit retention and require regular audits and redress mechanisms.
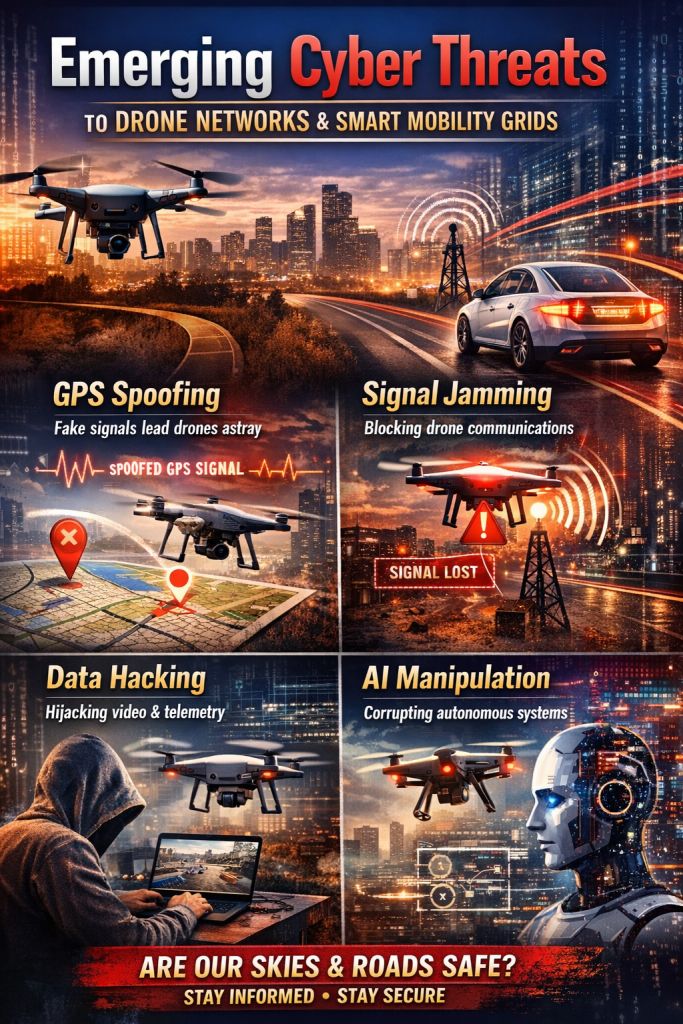
5. Regulating autonomous weapons: tech behind future wars
Autonomous weapons raise legal and ethical issues. International talks seek human oversight through treaties, as risks include software errors and a lack of transparency. Policies should mandate human involvement, clear standards, and export controls.
6. Children’s safety in the age of AI toys & smart devices
AI toys and connected devices for children capture sensitive data, raising privacy flags. Laws like COPPA apply, but rapid innovation outpaces enforcement. Parents and makers need practical guardrails.
Actionable steps for parents & makers:
- For parents: Restrict Wi-Fi access for toys, use guest networks, review permissions, read privacy policies, and choose reputable brands with transparent data practices.
- For product teams: Implement age-appropriate privacy defaults, such as minimal data collection and easy data deletion. Ensure clear parental consent processes and use strong encryption for communications.
7. How organisations can build compliance + trust — a concise roadmap
1. Data mapping & DPIAs — know what you collect, why, and how it’s moved. DPDP and EU law both make this non-optional for many entities.
2. Risk-based AI governance — adopt NIST (National Institute of Standards and Technology) AI RMF (AI Risk Management Framework) principles, document model provenance (origin history), and maintain incident playbooks (predefined procedures for responding to incidents).
3. Transparency & user control — intuitive consent, subject-access mechanisms, and explainability where decisions materially affect people.
4. Security & supply chain — patching, third-party audits, and contractual protections for data and models.
5. Cross-border playbook — implement data localization gates where required, and use standard contractual clauses or adequacy routes where possible.
8. A few real-world signals (why this is urgent)
The EU’s implementation of the AI Act and supporting codes of practice will begin to shape product design choices across industries.
UN-level momentum to discuss restrictions on autonomous weapons reflects geopolitical urgency — states and NGOs are already negotiating frameworks.
India’s DPDP Act imposes clear obligations on digital data fiduciaries — companies operating in or targeting India must adapt quickly.
1. Compliance Checklist for AI Models (LLMs, ML Systems, Predictive Models)
A. Governance & Documentation
☐ Maintain Model Cards (summaries detailing a model’s intended purpose, training data sources, known limitations, and identified risk areas)
☐ Keep full dataset lineage (documentation that tracks where data was collected, associated licenses, and how consent was obtained)
☐ Document model versioning, updates, and rollback procedures (methods for reverting to previous versions)
☐ Conduct AI Risk Classification (categorizing models as high-risk, general-purpose, or safety-critical based on legal definitions)
B. Legal & Regulatory Alignment
☐ EU AI Act: risk-based controls, transparency, logging, human oversight
☐ India DPDP Act: lawful basis, notices, consent, data fiduciary duties
☐ U.S. NIST AI RMF: risk management & bias mitigation
☐ Sectoral rules (healthcare, finance, mobility)
C. Data Privacy & Protection
☐ Perform Data Protection Impact Assessment (DPIA, an analysis to identify and minimize data privacy risks)
☐ Remove or minimize personal data in training sets
☐ Ensure privacy-by-design (privacy protections embedded within technology design, such as differential privacy, which adds noise to data to protect individuals, or anonymization, which removes identifying details)
☐ Implement dataset quality and bias testing
D. Safety, Bias & Performance Testing
☐ Conduct adversarial testing for prompt injection (deliberate manipulation of input to trick the model) and data poisoning (inserting corrupt data to influence outputs)
☐ Mitigate discriminatory outcomes using fairness benchmarks (standardized measures to check for bias)
☐ Conduct red-teaming (testing by simulated adversaries) for safety, hallucination (false outputs), and harmful outputs
☐ Maintain logs and documentation for auditability
E. Transparency & User Controls
☐ Provide users with clear notices that they are interacting with AI
☐ Implement explainability mechanisms for relevant decisions
☐ Enable opt-out options when applicable
☐ Publish model limitations and prohibited use cases
F. Security
☐ Secure model endpoints (API rate limiting, authentication)
☐ Encrypt training data, intermediate files, and outputs
☐ Regular vulnerability assessments
☐ Supply chain review (open-source models, dependencies)
G. Deployment & Monitoring
☐ Continuous monitoring for drift, accuracy, and harmful behaviors
☐ Incident response workflow for model failures
☐ Reporting process for vulnerabilities and misuse
☐ Regular audits and regulatory updates
2. Compliance Checklist for IoT Devices (Smart Home, Wearables, Sensors, AI Toys)
A. Hardware & Software Compliance
☐ Follow international device safety standards (CE, FCC, BIS)
☐ Secure boot + signed firmware
☐ Mandatory firmware update mechanism with rollback protection
B. Data Privacy (Critical for Kids’ Devices)
☐ Parental consent (COPPA, DPDP, GDPR Kids’ Data safeguards)
☐ Clear on-device privacy notices
☐ Data minimization: collect only what’s necessary
C. Connectivity & Network Security
☐ Encrypted communication (TLS 1.2+)
☐ Unique per-device credentials (no hardcoded passwords)
☐ Secure Wi-Fi onboarding flow
☐ Isolation modes for home networks
D. AI & Analytics Compliance
☐ Document data processing pipeline (the series of steps and locations, whether on-device or in the cloud, where data is handled)
☐ Provide explainability (tools to make automated decisions understandable to users)
☐ Enable data deletion, export, and consent withdrawal (give users control over their personal information)
E. Physical Safety + Child Protection
☐ No harmful materials or components
☐ Tamper-proof storage of sensitive data
☐ Provide “offline mode” (no data transmission)
☐ Age-appropriate defaults (mic/camera off by default)
F. Vendor & Supply Chain Controls
☐ Vendor risk audits for cloud services
☐ Signed components & third-party libraries
☐ Track provenance of chips, sensors, and firmware components
G. Post-Deployment Lifecycle
☐ EOL (End of Life) disclosure for security updates
☐ Vulnerability reporting program
☐ Automated logs for forensic analysis
☐ Regular third-party penetration tests
3. Compliance Checklist for Data Platforms (Cloud SaaS, Analytics Tools, Databases)
A. Data Governance & Ownership
☐ Maintain data inventory + flow maps
☐ Define lawful basis for all data processing
☐ Maintain retention and deletion schedules
☐ Role-based access controls (RBAC)
B. Privacy Laws Alignment
☐ India DPDP Act: notices, purpose limitation, user rights
☐ GDPR: consent, DPIA, DPO requirements
☐ U.S. sector laws (HIPAA, GLBA, CCPA, where relevant)
☐ Cross-border transfer compliance (SCCs, adequacy, localization)
C. Security Controls
☐ Encryption at rest + in transit
☐ Zero-trust architecture where possible
☐ Incident response plan with SLA timelines
☐ Authentication: MFA, SSO, password policy enforcement
☐ Infrastructure hardening & perimeter security
D. Data Quality & Minimization
☐ Validate and sanitize all incoming data
☐ Avoid collecting sensitive personal data unless necessary
☐ Anonymize datasets used for analytics
E. Logging, Monitoring & Auditability
☐ Centralized logging (SIEM)
☐ Automated anomaly detection
☐ Access logs retained as per regulatory requirements
☐ Annual security + privacy audits
F. Customer Rights & Transparency
☐ Easy dashboards for consent, data downloads, and deletion
☐ Publish privacy notices and subprocessors list
☐ Document all data-sharing activities
G. Business Continuity
☐ Data backup + disaster recovery plans
☐ Redundant geographic infrastructure
☐ RTO/RPO definitions for resilience
Final thoughts — technology governance as an opportunity
Regulation is not just a cost — it’s an opportunity to build trustworthy, competitive products. Companies that treat privacy, safety, and sovereignty as features will win loyalty and avoid fines. Policymakers who combine human-rights safeguards with clear technical standards enable healthier innovation. And citizens who demand transparency will push the ecosystem toward safer, fairer outcomes.